How to Defend Against AI-Powered Cyberattacks While artificial intelligence has revolutionized cybersecurity, it has also …

In today’s distributed digital landscape, security is no longer just about protecting a perimeter, it’s …
How to Control Cloud Costs Using a FinOps Framework Many organizations begin their cloud journey …
Building an AI-Ready IT Infrastructure: What Most Organizations Miss Artificial Intelligence is transforming how businesses …
How to Build a 90-Day DPDP Compliance Technology Roadmap India’s Digital Personal Data Protection (DPDP) …
How to Establish AI Governance Without Slowing Innovation Artificial Intelligence is enabling organizations to move …
The Evolving Landscape of AWS Storage: New Technologies and Endless Possibilities The cloud storage arena …
The Cloud Revolution Starts Here The era of cumbersome servers and perpetual data center expansions …
11 Types of Social Engineering Attacks Using deception and manipulation, social engineering attacks induce the target into …
CYBER RESILIENCE: 5 CORE ELEMENTS OF A MATURE CYBER RECOVERY PROGRAM Cyber resilience is the …
Container Adoption Trends: Why, How and Where Benchmark your application strategy with data. Read this …
Galaxy Recognised By The World HRD Congres As One Of The Dream Companies To Work …
The Five R’s Of Application Modernization Most organizations realize that application modernization is essential in order to …
Three Ways To Optimize Your Edge Strategy Enterprises can use these methods to move from …
5 Enterprise Tech Predictions Following An Unpredictable Year We all went into 2020 with a …
Multi-Cloud: Strategy Or Inevitable Outcome? (Or Both?) Multi-cloud is top of mind for many technology …
Dell’s 2021 Server Trends & Observations A summary of the top enterprise trends to look …
Top Tips For Securing The Remote Workforce In 2021 This year, organizations found an unprecedented amount of their workforces suddenly working …
Edge Computing As we move into a new decade of 2020, technological advancement is surely …
Cisco: 5 Hot Networking Trends For 2020 CISCO EXEC SAYS SD-WAN, WI-FI 6, MULTI-DOMAIN CONTROL, …
Tomorrow’s Forecast: Cloudy With A 90% Chance Of Containers Remember the old days—back in late …
Workspace One Vs VPN Organizations across the globe are becoming technology driven to remain productive …
HCI At The Extreme Edge Dell Technologies are introducing two new platforms to meet the …
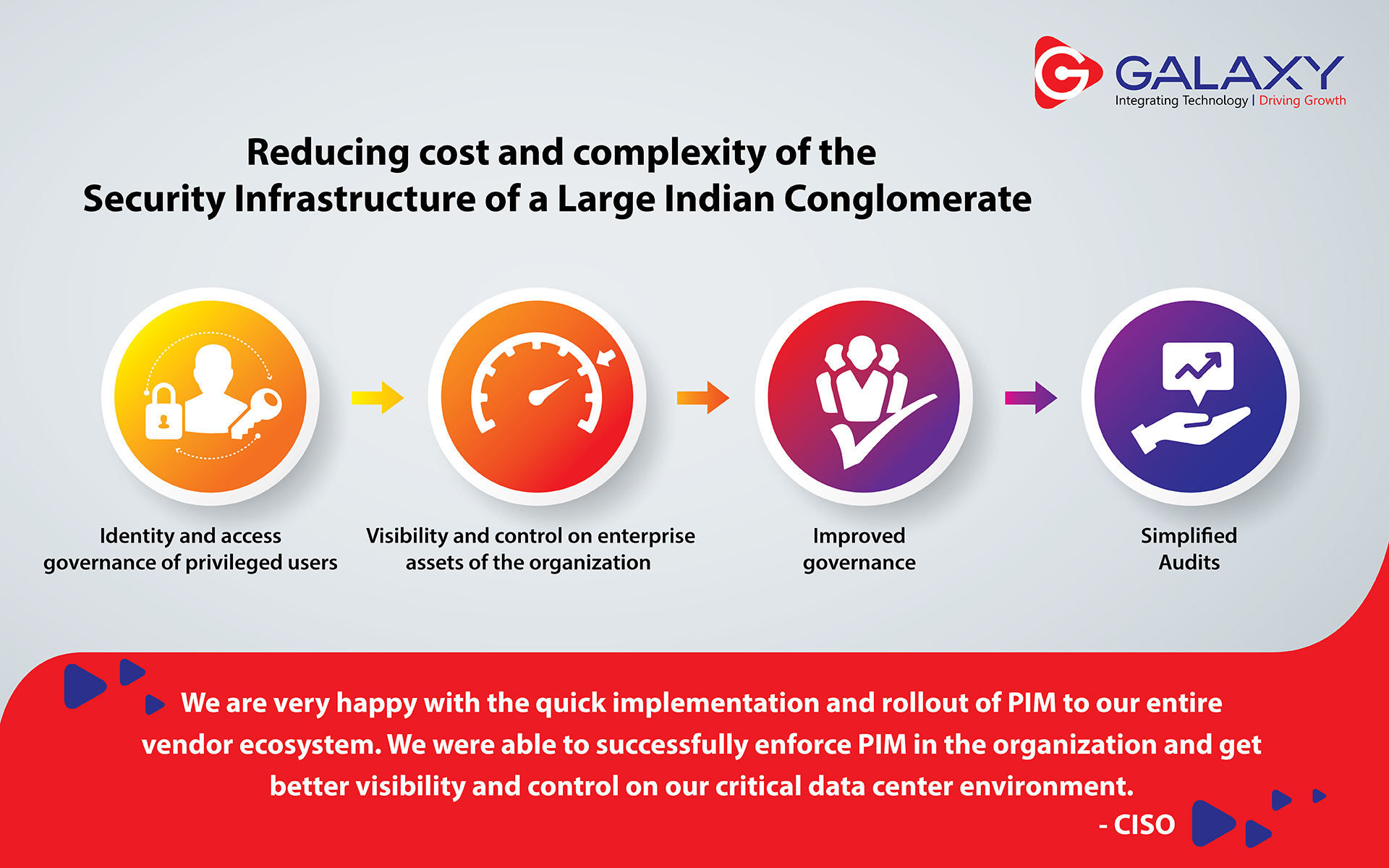
Privileged Identity Manager SECURING LEADING INDIAN CONGLOMERATE What’s the best way to reduce cost and …
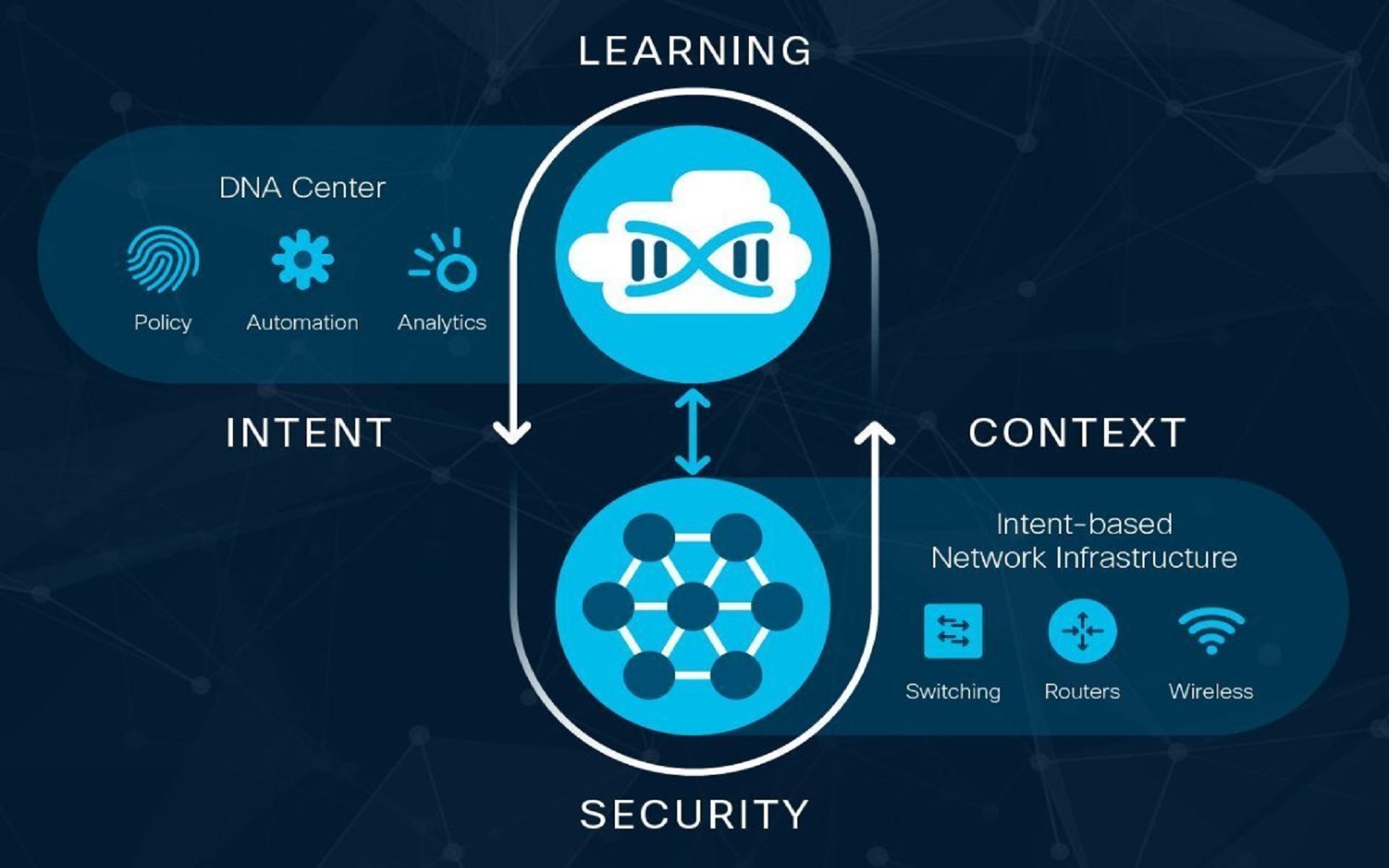
Software-Defined Networking A common question we receive is: “What is the relationship of software-defined networking …
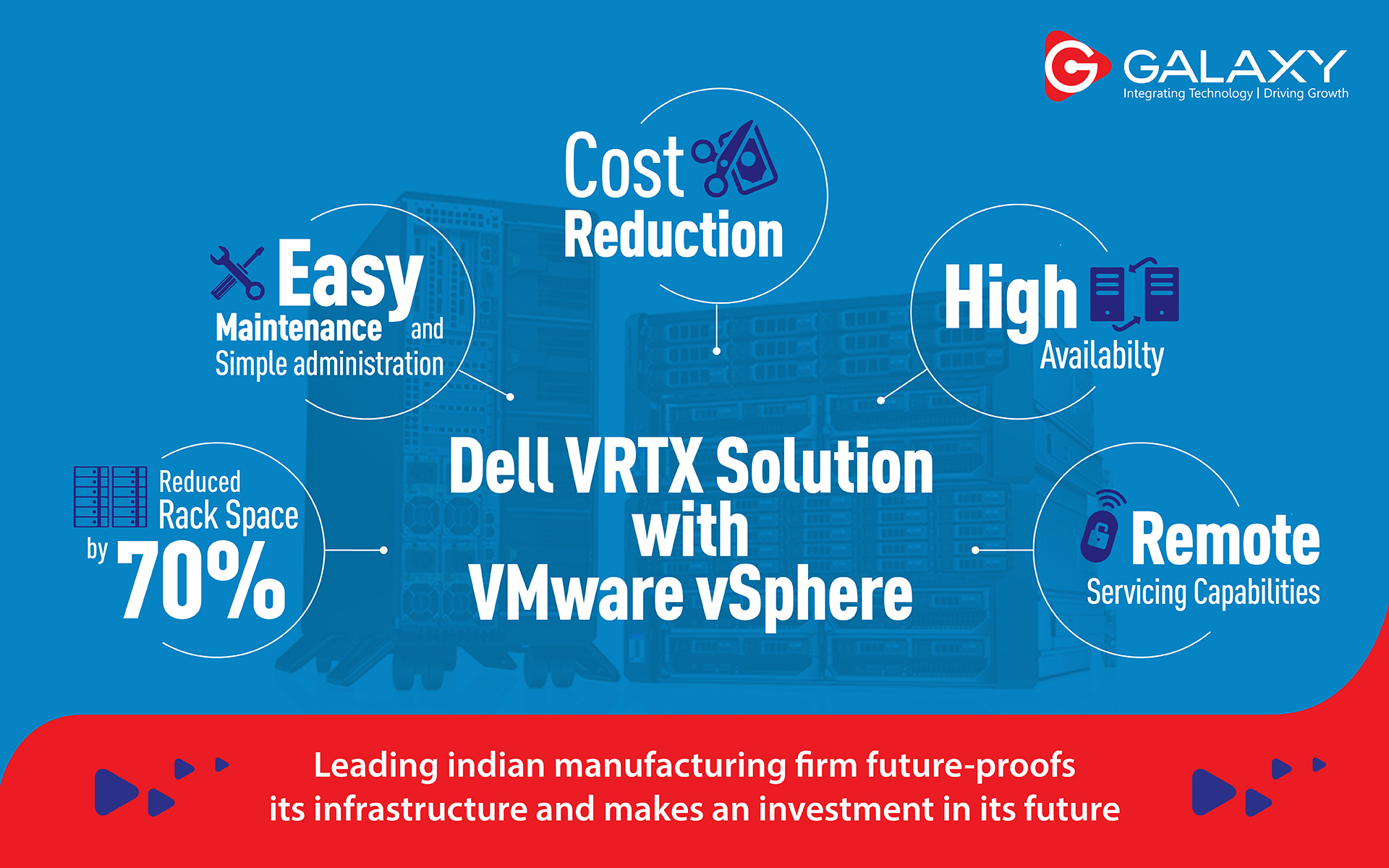
Dell VRTX Solution VMware VSphere LEADING INDIAN MANUFACTURING FIRM FUTURE-PROOFS ITS INFRASTRUCTURE AND MAKES AN …
BOTS As Employees, Busting The Myth BOTS AS EMPLOYEES, BUSTING THE MYTH Digital technology is …
Blockchain Technology LENOVO TRANSFORMS SUPPLY CHAIN OPERATIONS WITH BLOCKCHAIN Lenovo is a strong believer and …
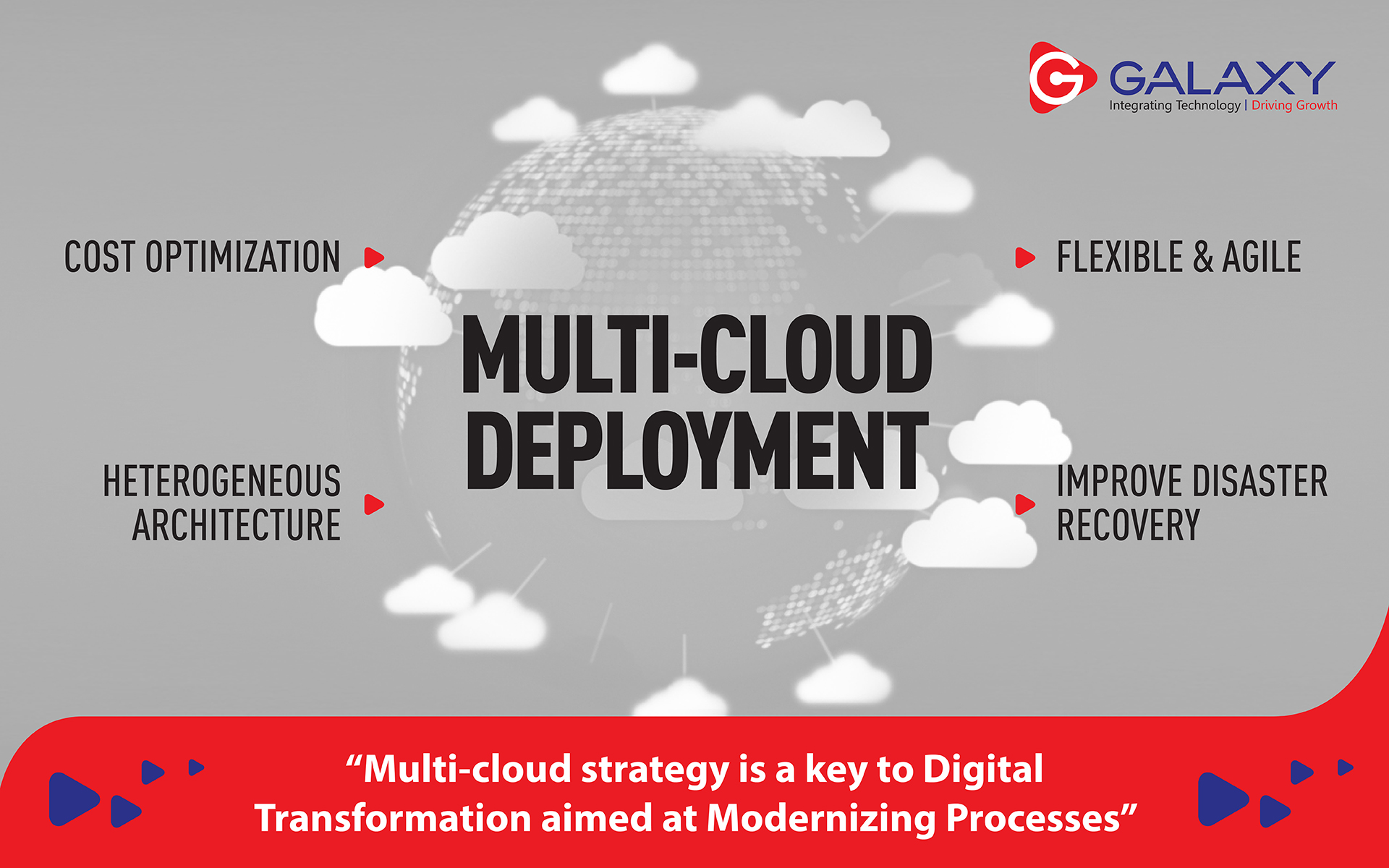
Multi-Cloud Deployment Planning MULTI-CLOUD STRATEGY IS A KEY TO DIGITAL TRANSFORMATION AIMED AT MODERNIZING PROCESSES …
Enterprise-Grade Kubernetes To The Data Center LENOVO AND GOOGLE: BRINGING ENTERPRISE-GRADE KUBERNETES TO THE DATA …
World Environment Day – Tree Plantation (Galaxy Collaborated With Grow-Trees) ON THE OCCASION OF WORLD …
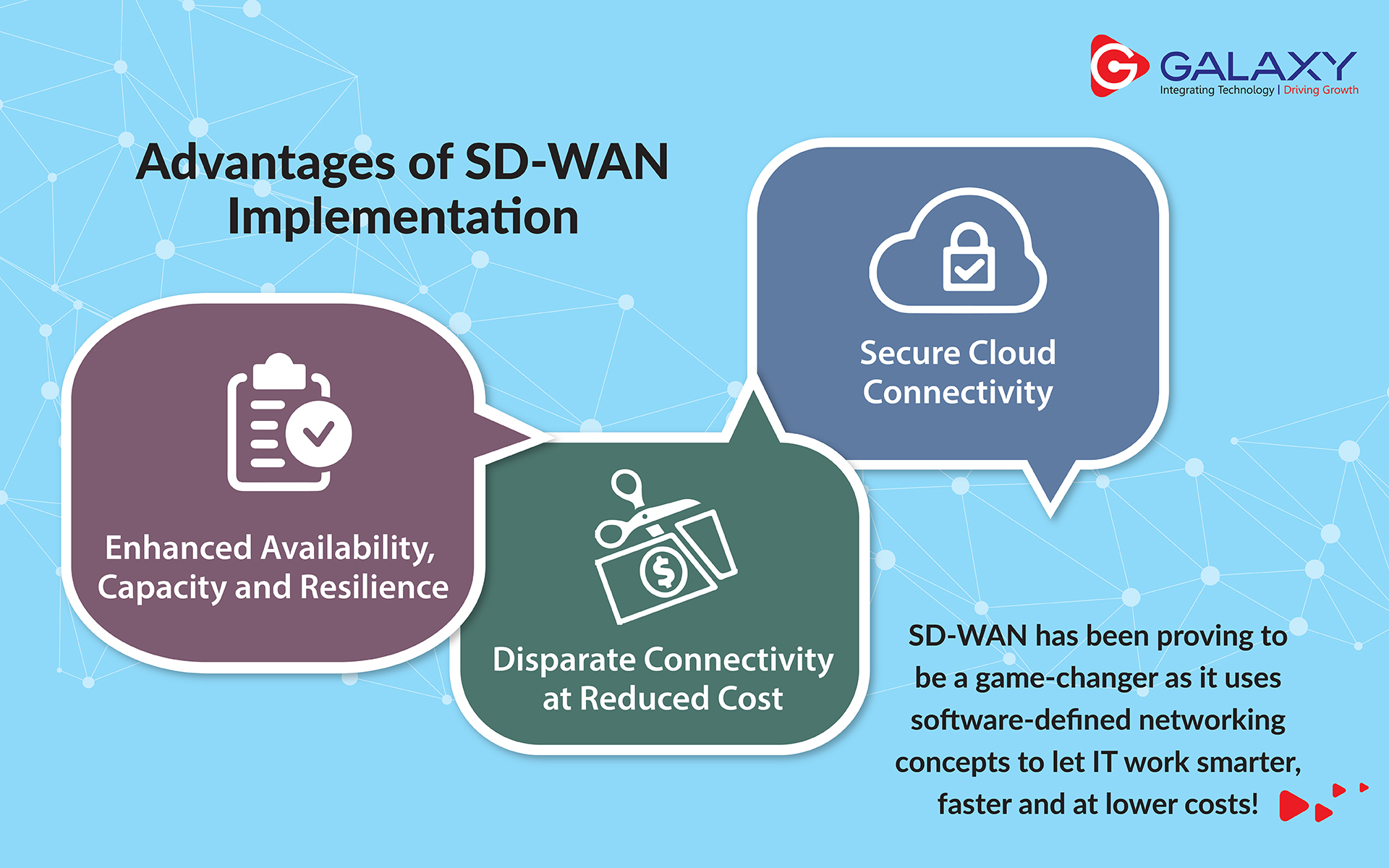
Advantages Of SD-WAN Implementation SD-WAN – WHAT ENTERPRISE IT LEADERS NEED TO KNOW As part …
Network Segmentation: Best Practices To Secure The Portal In the marvelous world of digital, enterprises …
Use AI To Simplify Distractions are the enemy of innovation. In order to be truly …
5 Critical Requirements For A Digital Workspace CHALLENGES OF A DIGITAL WORKSPACE As the digital …
How To Prevent Data Loss Of Your Company? Data loss prevention (DLP) solutions are growing …
The PowerEdge T40 –The Foundational IT Building Block For Your Business As a small business …
Intrusion Prevention (IPS) PROTECT AGAINST KNOWN, UNKNOWN, AND UNDISCLOSED VULNERABILITIES IN YOUR NETWORK The Cyber …
Robotic Process Automation We have been hearing a lot about automation and how it has …
Unified Endpoint Management Information Technology today has become an vital part of businesses today as …
Envisioning Cyber Security Future – 2020 In today’s connected world, everyone relies on technology more …
Hyper-converged Infrastructure Are you looking for intelligent, automated and simplified management of data? Know how …
Hyper Automation Technology today has changed the elementary facet of our lives. With urge for …