How to Defend Against AI-Powered Cyberattacks
While artificial intelligence has revolutionized cybersecurity, it has also armed adversaries with unprecedented capabilities. Attackers now utilize AI to execute high-speed, precision strikes, ranging from sophisticated, automated vulnerability discovery to hyper-convincing phishing campaigns that bypass traditional scrutiny.
In this shifting landscape, reactive security is no longer viable. To counter these intelligent threats, organizations must shift toward proactive, adaptive defense frameworks. This is where Galaxy delivers its greatest impact: providing the advanced, AI-driven strategies necessary to stay ahead of an increasingly automated threat landscape.
The Rise of AI-Powered Cyberattacks
AI-driven attacks are not theoretical—they’re already here and evolving rapidly. Key examples include:
- AI-generated phishing: Personalized, context-aware emails that are nearly impossible to distinguish from legitimate communication
- Deepfake impersonation: Voice and video spoofing used to manipulate employees or executives
- Automated vulnerability discovery: AI tools scanning systems at scale to find weaknesses faster than ever
- Polymorphic malware: Malware that continuously adapts its code to evade detection
These threats are dynamic, scalable, and increasingly difficult to detect using legacy systems.
Why Traditional Security Falls Short
Most conventional cybersecurity systems rely on static rules, known signatures, or reactive responses. This creates critical gaps:
- Slow detection of new or unknown threats
- Inability to adapt to evolving attack patterns
- Overwhelming false positives for security teams
- Limited visibility across distributed environments
In an AI-driven threat landscape, reactive defense is a losing game.
Galaxy’s Value Proposition: Security That Thinks Ahead
Galaxy addresses modern cyber threats with a fundamentally different approach—AI-powered, predictive, and autonomous security.
1. Proactive Threat Intelligence
Galaxy leverages advanced AI models to predict and identify emerging attack patterns before they materialize. Instead of waiting for threats to strike, Galaxy anticipates them.
Value: Reduced risk exposure and faster mitigation.
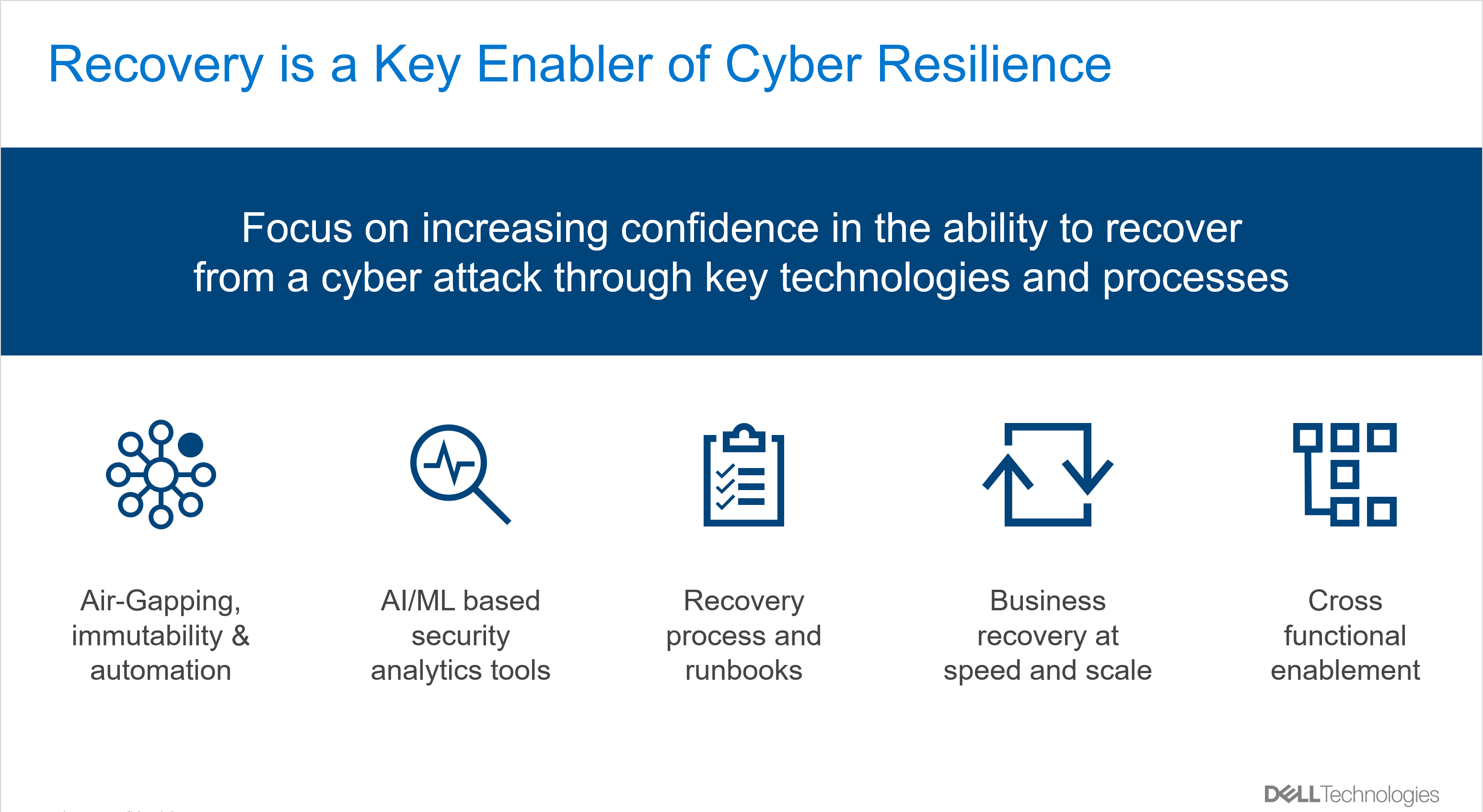
2. Real-Time Adaptive Defense
Galaxy continuously learns from network behavior, automatically adjusting its defenses in real time. This enables immediate response to anomalies and zero-day threats.
Value: Faster detection and containment with minimal human intervention.
3. Unified Security Visibility
Galaxy integrates across endpoints, cloud, and network layers, providing a centralized view of the entire attack surface.
Value: Improved situational awareness and streamlined security operations.
4. AI-Augmented Decision Making
Security teams are empowered with actionable insights, prioritized alerts, and automated workflows—reducing noise and improving efficiency.
Value: Higher productivity and better decision accuracy for security teams.
5. Built for Scale and Resilience
Galaxy’s architecture is designed for modern, distributed environments—handling large-scale data and complex infrastructures without compromising performance.
Value: Enterprise-grade protection that grows with your business.
Best Practices to Defend Against AI-Powered Threats
While Galaxy provides a strong foundation, organizations should adopt a layered defense strategy:
✔ Embrace AI for Defense
Use AI-driven tools to match the speed and sophistication of attackers.
✔ Implement Zero Trust Architecture
Continuously verify users and devices, regardless of location.
✔ Strengthen Identity Security
Deploy multi-factor authentication (MFA) and behavioral analytics.
✔ Conduct Continuous Monitoring
Real-time visibility is critical for early detection.
✔ Invest in Security Awareness
Train employees to recognize advanced phishing and social engineering tactics.
The Future of Cybersecurity is Intelligent
AI is reshaping the cybersecurity battlefield. Organizations that fail to evolve will find themselves increasingly vulnerable to automated, scalable attacks.
Galaxy’s approach ensures that businesses are not just reacting to threats—but staying ahead of them. By combining predictive intelligence, automation, and unified visibility, Galaxy empowers organizations to defend with confidence in an AI-driven world.
Stay ahead. Stay secure. Choose Galaxy.




 In today’s distributed digital landscape, security is no longer just about protecting a perimeter, it’s about securing identities, data and interactions across an ever-expanding ecosystem. As organizations navigate multi-cloud environments, remote work models and AI-driven operations, the need for a smarter, more adaptive security framework has become critical. This is where Galaxy steps in as a trusted solutions provider, helping enterprises build and operationalize a Cognitive Zero-Trust Fabric.
In today’s distributed digital landscape, security is no longer just about protecting a perimeter, it’s about securing identities, data and interactions across an ever-expanding ecosystem. As organizations navigate multi-cloud environments, remote work models and AI-driven operations, the need for a smarter, more adaptive security framework has become critical. This is where Galaxy steps in as a trusted solutions provider, helping enterprises build and operationalize a Cognitive Zero-Trust Fabric.
 How to Control Cloud Costs Using a FinOps Framework
How to Control Cloud Costs Using a FinOps Framework
 Building an AI-Ready IT Infrastructure: What Most Organizations Miss
Building an AI-Ready IT Infrastructure: What Most Organizations Miss
 How to Build a 90-Day DPDP Compliance Technology Roadmap
How to Build a 90-Day DPDP Compliance Technology Roadmap